LastPass, a password management service, sent a message to users urging them to update their master password to a “long string of 12 or more characters.” LastPass says its purpose is to “improve security,” but some experts have criticized LastPass’s response as “just performance and doesn’t make any sense in terms of security.”
LastPass Breach: Why These Password Duplicates Matter | Almost safe
https://palant.info/2022/12/28/lastpass-breach-the-significance-of-these-password-iterations/
LastPass: ‘Horse Gone Barn Bolted’ is a strong password – Krebs in security
https://krebsonsecurity.com/2023/09/lastpass-horse-gone-barn-bolted-is-strong-password/
Password management services like LastPass require you to set up a “master password” to access the password database. In 2018, LastPass added a restriction on the number of characters in a master password, stating that “all new master passwords created in the future must be at least 12 characters long.” In September 2023, LastPass added a character limit. Characters in the master password. Force update master password if
LastPass’s implementation of stronger master passwords comes after it was discovered in November 2022 that hackers accessed LastPass customer data.
It turns out that a hacker gained access to customer data using source code stolen from password management app “LastPass” – GIGAZINE
“Changing the length of your master password is not a response to customer data breaches that have already occurred, but rather a way to better protect your online databases,” said Karim Touba, CEO of LastPass. “This is to encourage users to stick with LastPass’s 2018 default setting.” is 12 characters or more.”
LastPass states that it does not store this master password, and asserts that if you lose the master password, it will be impossible to recover the database. But experts say that once you have access to the entire database, all you have to do is know the password.Brute force attackHe states that it is theoretically possible to access the database once it is decrypted
So, LastPass increases security by encrypting your master password multiple times. The more “iterations” this encryption takes, the longer it will take to crack the master password.
According to Mr. Palant, users who have been using LastPass for a long time said the number of iterations ranged between 1 and 500. However, since 2013, the default number of user occurrences has been 5,000 times, which increased to 100,100 times in February 2018, and has increased to 600,000 times in recent years.
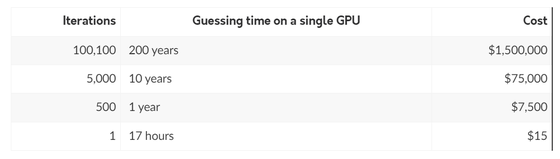
Palant calculates the analysis time and cost based on the number of coding iterations. When performing the analysis on a single GPU, if the number of iterations is 1, it can be analyzed at a cost of only 17 hours and $15 (about 2,200 yen), if repeated 500 times, it will cost 1 year and $7,500 (about 1,100,000 yen), and 5,000 times will require 10 years and $75,000 (about 11 million yen), and 100,100 times it would take 200 years and $1.5 million (about 220 million yen). So it can be said that redundancy of encryption greatly increases the security of the database.
However, users affected by the 2022 customer data leak said the encryption frequency settings on their accounts were never automatically upgraded. In other words, Palant criticizes that legacy users were left with only a few iterations of the encryption, making it less secure.
“LastPass made a big mistake by not forcing existing users to upgrade their encryption iterations,” said Nicholas Weaver, a researcher at the International Computer Science Institute at the University of California, Berkeley. The user is not criticizing LastPass, but LastPass is criticizing him. User saying: “You should have used a longer master password.”
Copy the title and URL of this article

“Travel maven. Beer expert. Subtly charming alcohol fan. Internet junkie. Avid bacon scholar.”







More Stories
Enjoy a hot cigarette while looking at whales and tropical fish under the sea ⁉︎ “Ploom Dive” is an amazing spatial video experience using Apple Vision Pro
Apple Watch now supports sleep apnea, watchOS 11 released – Impress Watch
ASCII.jp: New macOS Release! macOS Sequoia 15 Can Display Your iPhone Screen on Your Mac!