iMobie Inc. AnyFix updates to version V2.2.4.0 on Tuesday, April 23, 2024. This latest update adds new features to solve...
Spotify Technology (SPOT) reported fiscal first-quarter earnings on Tuesday that beat expectations on both the top and bottom lines. The...
Welcome to Wordle Review. Be warned: This page contains spoilers for today's mystery. Solve Wordle firstOr scroll at your own...
The most distant spacecraft on Earth, Voyager 1, has begun communicating properly again with NASA after engineers worked for months...
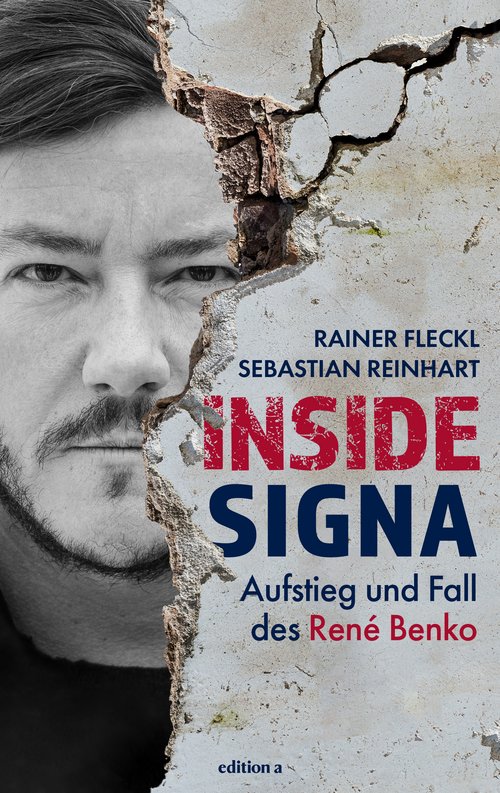
Inside Signa by Rainer Flickl and Sebastian Reinhart provides a detailed study of the rise and fall of businessman Rene...
For many years, Newburgh local councils have been grappling with the possibility of developing and using Church Field. Now nothing...
EA and Amazon Prime have released the seventh game pack for the current season of FC 24. We'll be bringing...
The original Famicom was manufactured in Game Boy sizeConvert it into a mobile game machineMac mini from AppleMake it more...
SAN FRANCISCO - Google has fired about 20 additional workers that it said participated in protests denouncing the company's cloud...
The heat for Season 22 of "American Idol" is heating up, and so are the judges' criticism as the competition...